Viac ako 10 rokov osvedčenej bezpečnosti, pravidelné nezávislé certifikácie vo viacerých krajinách NATO v kombinácií so silným šifrovaním udržujú vaše informácie v bezpečí za každých okolností.
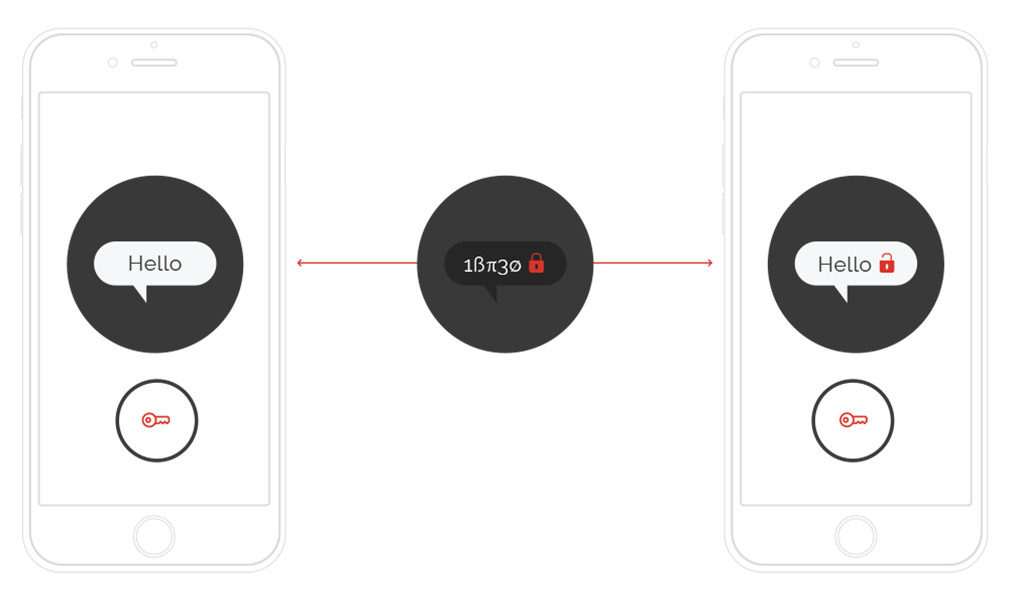
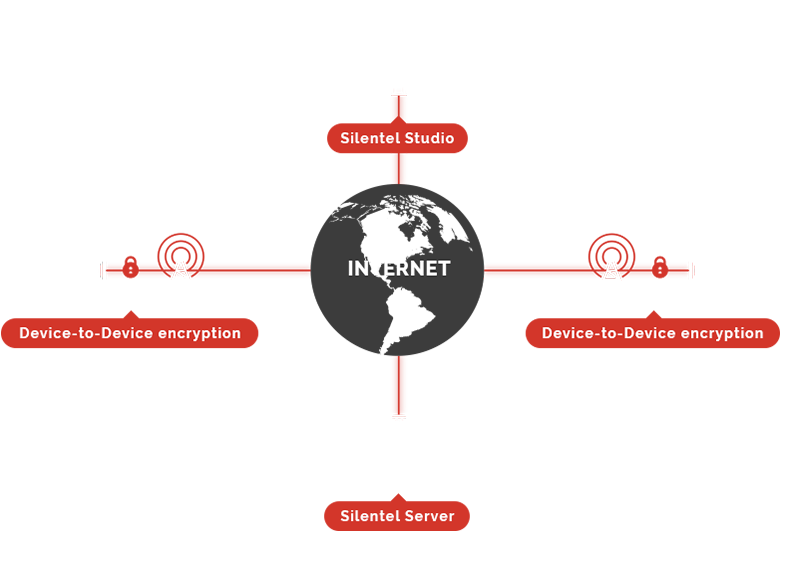
Komunikácia je pred odoslaním zašifrovaná a dešifrovaná až po prijatí príjemcom (priamo v zariadení používateľa). Dáta nie sú nikdy počas prenosu dešifrované. Dokonca ani Silentel Server nikdy nepozná šifrovacie kľúče a nie je schopný dešifrovať obsah komunikácie.
Každá komunikácia je chránená unikátnym šifrovacím kľúčom, ktorý je generovaný na začiatku komunikácie. To znamená, že každá komunikácia medzi dvoma používateľmi, rovnako aj každá komunikácia medzi rovnakými dvoma užívateľmi, má svoj jedinečný šifrovací kľúč, ktorý nie je možné predvídať. Každý šifrovací kľúč je zničený bezprostredne po ukončení komunikácie.
Žiadne informácie a to vrátane zoznamu kontaktov sa neukladajú v mobilnom zariadení. A tak aj v prípade straty, či odcudzenia telefónu všetky dáta a informácie ostávajú nedostupné a navždy chránené aplikáciou Silentel. To znamená, že žiadna forenzná analýza neumožní získať žiadne citlivé informácie (ako napr. hlasové hovory, textové správy, súbory a kontakty) zo zariadenia používateľa.
Telekomunikační operátori ukladajú veľké množstvo osobných údajov o svojich užívateľoch, ich komunikáciach a informáciach a ich polohe. Silentel systém nevyžaduje žiadne osobné údaje (meno, adresu, GSM číslo, polohu ani nič podobné). Silentel komunikácia je prenášaná vždy ako internetové dáta (ako v prípade používania internetu), čím sú vaše hovory a textové správy nevystopovateľné.
Silentel je celosvetovo prvou mobilnou bezpečnostnou platformou, ktorá spĺňa všetky bezpečnostné požiadavky NATO a je zaradená v zozname NATO produktov v oblasti informačnej bezpečnosti (NATO Information Assurance Products Catalogue - NIAPC).
Od roku 2006 je Silentel certifikovaný Národným bezpečnostným úradom na Slovensku a ďalšími bezpečnostnými úradmi v zahraničí, pre bezpečnú mobilnú komunikáciu pre stupne utajenia VYHRADENÉ a DÔVERNÉ.
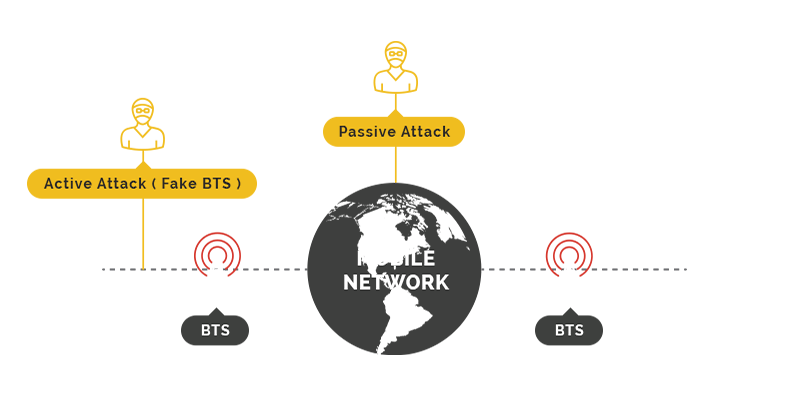
Nedostatky návrhu v štandarde GSM umožňujú používať falošné mobilné veže medzi cieľovým mobilným telefónom a skutočnými vežami. Existuje mnoho ukážok a manuálov, ako vykonať takéto útoky pomoci opensource softvéru a bežne dostupného hardvéru za cenu niekoľkých tisíc eur.
Vedeli ste, že GSM signál je vždy šifrovaný? Bohužiaľ, šifrovanie je tak zastaralé a slabé, že existuje niekoľko techník, ktoré umožňujú dešifrovať vašu komunikáciu s 99% úspešnosťou.
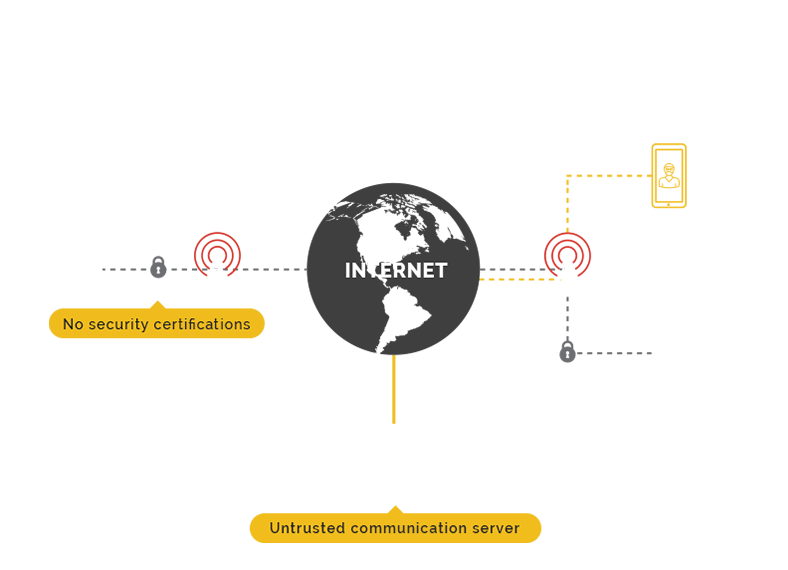
Prvým a najdôležitejším faktorom, ktorý je potrebné zvážiť v súvislosti s bezpečnosťou je, či je k dispozícii bezpečnostné hodnotenie tretej strany. Bez toho môže dodávateľ použiť akýkoľvek druh bezpečnostného mechanizmu, pretože klient nemá možnosť ako to overiť alebo dokázať opak.
Väčšina šifrovacích aplikácií používa centrálny komunikačný server. Tvrdenia, že aplikácia používa šifrovanie typu end-to-end, sú zbytočné, keď je komunikačný server je schopný zachytiť alebo rekonštruovať šifrovací kľúč alebo môže vynútiť re-šifrovanie správy.
Väčšina šifrovacích aplikácií umožňuje otvorenú registráciu. V tomto prípade - Ako môžete ovládať svoju komunikačnú skupinu? Ako si môžete byť istý ohľadom identity kontaktov? Ako sa môžete vyhnúť posielaniu správ neoprávneným osobám s falošnou identitou?
správa užívateľov a komunikačných skupín prostredníctvom jednoduchého web rozhrania.
Zistiť viacnikdy nepozná šifrovacie kľúče a nie je schopný dešifrovať obsah komunikácie.